This is the third and final article in our series on monetizing desktop software. The first part looked at pricing considerations and the second at how to sell through e-commerce channels. This part looks at how to protect your revenue and investment from pirates and reverse engineers looking to steal your intellectual property (IP).
With software piracy costing businesses $46B annually, taking steps to protect your investment is key to sustaining your revenue and growing your business.
This article explores the risks from piracy (which stretch further than simply lost revenue) and steps you can take to help ensure that value is preserved long-term.
Software piracy is often treated as a revenue problem: lost sales, lost licenses, lost opportunity. While those impacts are real, they only tell part of the story. In practice, software piracy creates a wide range of risks that affect not just software vendors, but also customers, partners, and entire ecosystems.

Software is easy to copy and distribute digitally. Without strong protection, this makes piracy easy too. For many businesses, especially those selling desktop or professional software, this creates exposure that goes far beyond simply lost income.
The most obvious risk of piracy is financial. When software is used without a valid license, vendors lose direct revenue. Over time, this can significantly affect cash flow, pricing strategy, and investment decisions.
Piracy also distorts the market. When some users get the product for free, paying customers may question pricing or fairness. This can cause pressure from legitimate customers and force vendors to lower prices or reduce features. For smaller companies, sustained piracy can threaten long-term viability and make it harder to fund development, support, and innovation.
Software piracy is not just about free use. In many cases, software is reverse engineered, modified, or repackaged. This exposes proprietary algorithms, workflows, and techniques that represent years of research and development.
Once intellectual property is extracted, it can be reused by competitors, embedded into counterfeit products, or resold under different branding. Unlike physical goods, stolen software can be duplicated endlessly at near-zero cost. Once IP escapes, it is almost impossible to recover.
Pirated software is a major security risk for users. Unofficial downloads are one of the most common ways malware is distributed. Attackers often bundle ransomware, spyware, or backdoors into cracked installers.
For businesses, this creates a hidden cost. Users running pirated software may still seek support, report bugs, or blame the original vendor when something goes wrong. Worse, compromised systems can lead to data breaches, regulatory violations, and reputational damage — even if the vendor had no direct involvement.
Piracy weakens brand control. Modified or cracked versions of software may behave unpredictably, crash more often, or disable safety features. When users encounter problems, they often associate them with the brand, regardless of the fact they are running an illegal copy.
This is especially serious for professional, creative, or safety-critical software. Poor performance or failures caused by tampered versions can erode trust and damage a reputation built over years. In regulated industries, such as healthcare or engineering, misuse of pirated software can also create legal and ethical concerns.
Ironically, piracy often increases costs for vendors. Support teams spend time dealing with issues caused by unauthorized copies. Engineering teams may need to respond to exploits used to bypass protections. Sales teams must manage pricing pressure caused by widespread illegal use.
All of this diverts resources away from improving the product for legitimate customers.
Given the risks that software piracy and reverse engineering bring to your business, it is important to protect your software. This makes software licensing one of the most important tools for protecting revenue. At its core, licensing defines who can use your software, how it can be used, and for how long.
Software licensing should be there to support your business so what are the key considerations when choosing a platform?

Modern customers expect instant access after purchase, with no manual steps or delays. Licensing systems must integrate cleanly with e-commerce platforms so that every transaction reliably triggers license creation and delivery. Manual fulfillment may work at small scale, but it quickly becomes expensive, error-prone, and difficult to support as transaction volumes grow. Automated licensing reduces operational cost while ensuring every user receives exactly what they paid for.
Another important factor is flexibility. Users upgrade machines, work offline, and move between environments. Licensing systems should support these real-world workflows with features like license transfers, offline activation, and device limits. When licensing is too rigid, customers look for ways around it. When it’s well designed, it becomes an enabler rather than a barrier. The goal is to raise the cost of abuse without punishing legitimate users.
A licensing platform’s ease of deployment and support overhead is key in maintaining engineering velocity and allowing your business to scale. A system that is difficult to integrate, configure, or maintain will slow down releases and increase the burden on engineering and support teams. Developers need licensing tools that fit naturally into existing build, CI, and release pipelines.
Just as important is what happens after launch: licensing issues have the potential to become a common source of support tickets. A good licensing platform reduces support overhead by handling common scenarios like activations, machine changes, offline use, and recoveries in a self-service way, allowing support teams to focus on real customer issues instead of fixing licensing problems.
Desktop developers also need to think about the strength of protection a licensing platform provides. A license that can be easily bypassed offers little real protection. Basic serial numbers or simple file checks are often shared online within days. Effective licensing should be tightly integrated into the application, making it difficult to remove without breaking functionality.
PACE’s iLok Licensing is designed specifically for long-lived, professional desktop software. It provides:

Software developers choose iLok because it provides proven, professional-grade licensing that protects software revenue without disrupting legitimate users. With flexible license models, strong anti-piracy protection, and seamless integration into desktop workflows, iLok lets developers focus on building great software while maintaining control over how it’s sold and used.
Protecting your software is ultimately about protecting the value you’ve worked to create. Pricing and e-commerce determine how customers buy, but licensing determines whether that value holds over time. Without strong protection, piracy, reverse engineering, and misuse can quietly erode revenue, increase support costs, and weaken trust in your product. A well-designed licensing strategy helps ensure that the customers who benefit from your software are the ones who support its continued development.
For desktop software developers, licensing needs to do more than block abuse. It must scale with your business, integrate cleanly with your sales channels, and support real-world workflows without frustrating legitimate users. Automation, flexibility, ease of deployment, and strong security all play a role. When these pieces work together, licensing becomes an enabler. It supports growth, simplifies operations, and preserves intellectual property.
If you’re looking for a proven way to protect your revenue and investment, learn more about iLok Licensing from PACE. Designed specifically for professional desktop software, iLok helps you secure your IP, reduce support overhead, and deliver a smooth experience for your customers. Visit the iLok Licensing page to see how it can support your monetization strategy and help safeguard your business for the long term.
Go back to part two: e-commerce

Download the iLok Licensing product brochure to learn more about how PACE's software licensing platform protects your IP and allows you to maximize your value.
This is the second part in our series on monetizing software. Part one looked at pricing. This article focuses on how to sell through e-commerce channels.
Selling desktop software has changed over the years. Traditionally, individual customers would buy a physical copy of the software and license; while selling to enterprises meant invoices, resellers, and manual delivery of licenses. Those approaches still work in some markets, but customer expectations are changing.
Today, even professional users expect to be in control of their buying experience. That means being able to discover, evaluate, and purchase software online. As a result, many desktop software vendors are moving toward e-commerce channels to support direct digital sales. Some are building in house while others are utilising e-commerce platforms such as WooCommerce and Shopify.
This shift creates clear benefits but it also introduces new technical and operational challenges. This article looks at what changes when you adopt e-commerce, what you need to put in place, and how digital distribution fits into the picture.
E-commerce fundamentally alters how customers buy your product. It moves from human managed processes to self-service driven by automation.
Even in enterprise sales, where human interaction is still important and a full e-commerce approach isn’t appropriate, there is still a desire to increase automation and speed up processes.
Instead of long sales cycles and manual onboarding, customers now expect:
At the same time, vendors face:
For desktop software, this means billing, licensing, and fulfillment must all operate reliably without manual intervention.
Before launching e-commerce for desktop software, several foundations must be in place.
We’ve all bought products online. The interface where you browse, select and pay is the online store or marketplace. If you wish to sell your software products online, then you’ll need an online marketplace. This may be tightly integrated with your website, a separate portal under your control, or selling through someone else’s marketplace.
The marketplace will need to:
You also need to decide if you want to offer free trials; and if so, will they be managed through your marketplace.
The same is true for subscriptions. Will renewals be handled through your marketplace or another channel?
The next question you need to answer is how unique do you need your store to be? Unless you are Amazon, you are unlikely to build all of your store from scratch, you will be using third-party services and components. The result you are looking for is a smooth buying experience (friction = lost sales) that reflects your brand. The more you can achieve that with off-the-shelf components, the better.
One thing to make sure is that the components you select can handle digital products. Many are focused on selling physical goods.
An important part of selling desktop software online is distributing the license. Every online sale must trigger a reliable entitlement process.
This is because while digital distribution increases reach, it also increases risk. Once installers are publicly accessible, they can be:
Put simply, software is easy to pirate and distribute, and intellectual property is straightforward to steal.
Proper controls protect against piracy. Manual fulfillment breaks down quickly at scale and creates support overhead. Therefore, effective digital distribution requires license and protection mechanisms that scale with your business. That means they need to integrate with your e-commerce marketplace and work reliably without human intervention.
WooCommerce and Shopify are two of the most popular e-commerce platforms.
Many desktop software vendors use WooCommerce, often because it integrates naturally with existing WordPress-based websites and content workflows. Others prefer Shopify for its speed of setup and hosted infrastructure.
Both platforms offer:
However, neither platform natively understands software licensing. This is one reason PACE introduced its iLok Licensing Delivery App for Shopify. The Shopify app allows vendors to:
The result is a smoother purchasing experience without weakening licensing or protection.
E-commerce customers expect immediate access to software after purchase. As discussed above, that means receiving the licensing they paid for. It also means being able to download the software’s installer.
In e-commerce, the Merchant of Record is the party that legally sells a product to the customer. This matters more than many businesses realize. If you sell software, digital services, subscriptions, or physical goods online, you need to know who carries this role. The Merchant of Record is responsible for charging sales tax or VAT, handling payments, managing refunds and chargebacks, and meeting local consumer-protection laws. That means compliance with tax rules across countries and states, secure payment processing, and accurate financial reporting. Startups, digital marketplaces, and anyone selling internationally should care deeply about this, because getting it wrong can lead to fines, blocked payments, or forced changes to how you sell.
If it sounds scary, third parties exist that act as the Merchant of Record on behalf of software developers. They often provide a wider e-commerce platform that can take on a lot of heavy lifting discussed in this article.
E-commerce has become a natural extension of how desktop software is sold. Customers now expect speed, clarity, and control, while vendors need systems that operate reliably at scale. Moving sales online replaces manual processes with automation, but it also removes many of the safety nets that traditional sales models relied on. That’s why e-commerce reshapes how billing, licensing, delivery, and compliance work together behind the scenes.
To succeed, software vendors need solid foundations. A smooth online marketplace must connect cleanly to automated licensing and secure digital distribution. Each purchase should trigger entitlement without delay, while still protecting intellectual property from misuse or theft. At the same time, decisions like who acts as the Merchant of Record have legal and financial consequences that extend far beyond checkout.
E-commerce can unlock global reach, faster revenue, and a better customer experience — but only when it’s designed for software, not adapted from physical retail. In the next part of this series, we’ll look more closely at licensing, protection, and how to maintain control once your software is being delivered digitally at scale. Because selling online is easy; selling securely and sustainably is the real challenge.
Continue to part three: Protecting your revenue and investment
This is the first in a three part series discussing software monetization. The series will focus on the oft-overlooked area of desktop software; and starts with how to price your software.
Choosing how to price your software is one of the hardest decisions you can make as a product team. Pick the wrong model, and customers might never bite. Set the wrong price, and you leave money on the table or, worse, chase customers away.
In this article we’ll break down common pricing models and give you a simple, practical way to think about how to choose between them and how to set the price point.
Good pricing does three important things:
Whether you are targeting enterprise, prosumer, or consumer markets, the answer shouldn’t be “just pick a number.” It’s about picking a model that matches how customers use and value your software.
Pricing desktop software is fundamentally different from pricing cloud services. Once your software is shipped as a binary, it can be installed, copied, and run in environments you may never see. That reality shapes every pricing decision you make.
Pricing desktop software is different because the software often runs:
Once delivered, the software may remain in use for years without connecting to the internet. This means pricing models that require “phoning home” for license enforcement may not work. For example, if a subscription needs an internet connection to renew, then that could be problematic is a truely air-gapped environment.
As a result, desktop software pricing and licensing are closely linked. A pricing model that cannot be enforced reliably will leak revenue, no matter how well it looks on paper.
Unless your software requires a unique pricing model, it is a good idea to select from the common models in use today. Doing so means your potential customers will find your pricing familiar and easy to understand. This reduces friction in the buying process.
The most common models you’ll see in software today are:
A perpetual license allows customers to buy the software once and use it indefinitely.
It works well when:
Perpetual licenses are still common in engineering tools, creative software, and specialist utilities. The benefit is that you get the money upfront, but the trade off is that revenue stops after the sale unless upgrades are paid for separately.
This hybrid model combines a one-time license fee with an annual maintenance or support contract.
Maintenance typically includes:
Customers keep their licensed version forever, but must renew maintenance to stay current.
If considering a hybrid model, extra consideration needs to be given to revenue enforcement. For example, PACE offers Release Date Limits (RDL) which can be used to limit a customer to versions of your product from a given date range. This allows a perpetual license to be given to the user but only binaries with a specified release date will run. This enables you to provide perpetual licenses that limit updates and maintenance releases to a timeframe of your choice. In other words, it allows you to sell perpetual licenses while monetizing time limited support contracts.
A hybrid perpetual plus maintenance model offers a balance between customer control and vendor sustainability and remains one of the most effective approaches for professional desktop software.
Subscription models charge customers regularly to continue using the software.
For desktop products, subscriptions mean:
To work well, subscriptions for desktop software rely on strong licensing to enforce subscription policies and terms. That strong licensing needs to have in-built subscription support (e.g. grace periods) to avoid unnecessary customer friction.
Subscriptions work best when regular updates deliver clear ongoing value and renewal processes are automated.
A Rent-to-Own (RTO) license is a hybrid licensing model that allows users to make recurring payments for software over time with the option to gain full ownership after a certain number of payments.
For desktop products, rent-to-own means:
This model appeals to users who want to eventually own the software but may not be able to afford a large upfront purchase. Rent-to-Own licensing systems must be capable of tracking payment milestones, transitioning licenses from temporary to permanent status, and enforcing conditions during the rental period.
Many desktop products offer multiple editions with different capabilities.
For example:
This allows you to serve different customer segments without fragmenting the product.
There’s no single answer that fits every product; and product success is about meeting the needs of customers rather than simply following the competitions. Therefore, instead of starting with trends, a good approach is to start with constraints. Begin by asking yourself:
If your software must run fully offline or in controlled environments, perpetual or hybrid models are often more realistic than pure subscriptions.
If customers expect frequent updates, subscriptions or maintenance renewals become easier to justify.
How do your customers prefer to buy? Professional users often compare your pricing to established tools in their field. A pricing model that feels out of place can block adoption, even if the product is strong.
Talk to customers early. Resistance to pricing models needs to be taken seriously.
If steady growth and forecasts matter, subscription models are generally stronger than perpetual as by their nature they deliver recurring revenue. Even enterprise tools are moving to subscription for this reason.
The challenge with perpetual licensing is that it can be hard to generate follow-on revenue for customers. When deploying a perpetual model thought needs to be given to how to generate additional revenue e.g. Will you charge for maintenance? Do you intend to release new versions which will require an upgrade fee on a regular basis?
Once you have a model, you need a number: the price. The aim is to get that number to match the perceived customer value.
Step 1
Customer Value
Step 2
Market Anchors
Step 3
Test & Learn
Here’s a simple framework:
You are the expert in your software. You know why you built it and the use cases it enables. If you haven’t already, now is the time to think about what those use cases mean in monetary terms. Ask yourself:
The point here is that price should be a fraction of the value delivered, not a reflection of development cost. Let’s be clear, your potential customers don’t care what it costs to build the software, what they are willing to pay for is the value it brings to them.
To put that another way, “cost-plus” models don’t optimize your revenue. If the cost is greater than value, then customers simply won’t buy (and you have a bigger problem!). If cost-plus is lower than the value, you are leaving money on the table.
Find similar products and compare your estimated customer value to their pricing.
This anchors your pricing to market reality. Which helps avoid pricing that feels arbitrary or disconnected from expectations.
The first two steps have given you a pricing hypothesis – a pricing model and price point that feels right but hasn’t been market tested. The next step is to test the pricing by talking with target customers.
It’s maybe stating the obvious, but don’t ask customers how much they’d pay. You need to be more subtle and triangulate multiple data points to find the right price point.
For example, as price is often a quality indicator to buyers, you can present a price point and ask about how it aligns with the perceived quality of your product.
Price testing shouldn’t stop when you launch your product, in fact, it’s really only the beginning. You need to continuously monitor:
Don’t think of pricing as a one-time decision. It’s about constantly learning and adapting. Start by choosing a model that aligns with how your customers use and value your software, then set your price by estimating value, checking the market, and testing with real users.
Good pricing helps you grow sustainably. The best pricing models align customer expectations, licensing realities, and sustainable revenue. When those three are in balance, pricing can be a strength to your business.
Continue with part two: e-commerce
Skip ahead to part three: protecting your revenue and investment




Download the iLok Licensing product brochure to learn more about how PACE's software licensing platform protects your IP and allows you to maximize your value.
Artificial Intelligence (AI) is quietly changing how medical devices work. Not long ago, most devices simply measured and reported data. Today, many of them think locally. Thanks to embedding AI in medical devices, they can spot patterns, predict risks, and help guide treatment in real time.
This shift is powered by embedded AI. Instead of sending data to the cloud, AI models now live inside the device itself. ECG monitors can learn a patient’s normal heart rhythm. Imaging tools can flag early signs of disease. Wearables can adjust therapy on the fly. The result is faster decisions, better privacy, and more personalized care.
But there’s a catch. When AI moves into devices that can be physically accessed, it can be copied, manipulated, or reverse-engineered. In short, it becomes exposed; and in healthcare, exposure is more than a technical problem, it’s a clinical one.
The global medical device market will be approaching one trillion dollars by 2030, with AI-driven systems leading the way. For manufacturers, this creates a huge opportunity.
The real value of many devices no longer rests in the hardware. It is in the trained AI model: the data, logic, and experience baked into the algorithm. These models can take years to build and millions of dollars to refine.
As devices become smarter and more connected, they become more attractive targets for threat actors. Embedded AI faces real threats:
Each of these attacks harms business value: competitive advantage, revenue, and investor confidence. Some of them can also put patients at risk.
In medical devices, security failures don’t stay theoretical.
If an attacker alters an AI model, diagnostic accuracy can fall. If software is changed, safety checks may fail. Even copying a model and redeploying it elsewhere can lead to unpredictable results. That’s why regulators are paying attention.
The FDA, EU MDR, and international standards bodies now treat cybersecurity as part of medical safety. Compliance alone only sets the minimum bar. Attackers move faster than regulations. Real protection has to be designed in from the start.
Many developers still rely on encryption or basic obfuscation to protect their embedded AI.
Unfortunately, these approaches were never designed for modern AI models. Often, AI models are effectively just data files running on standard frameworks. If the model or its decryption key can be found, it can be copied. If it can be inspected at runtime, it can be manipulated.
In short: if your model runs “in the clear,” it isn’t protected.
Effective protection means treating AI models, code, and cryptographic keys as a single inseparable unit. PACE approaches this by:
This kind of architecture prevents both static and dynamic attacks, even when devices are physically accessible.


In healthcare, trust matters. A protected AI model delivers consistent results, supports regulatory confidence, and reduces the risk of recalls or downtime.
More importantly, it protects what truly matters:
Embedded AI is transforming medicine. But only secured AI can be truly trusted.
In the future of connected healthcare, the strength of your protection may matter just as much as the intelligence of your algorithms.
Embedded AI is reshaping healthcare; but innovation without protection puts both revenue and patient safety at risk. Understanding the threats, regulations, and security architectures involved is the first step toward building trusted, resilient medical devices.
To explore this topic in more depth, download our full white paper: Embedded AI: Medical Device Opportunity and Security Challenge
It covers:
Download the white paper here:
https://paceap.com/digital-health/embedded-ai-medical-device-white-paper-download/
AI models are valuable intellectual property (IP). They often represent years of work, money, and expertise. If these models are stolen, copied, or misused, companies lose their competitive edge and revenue.
At PACE Anti-Piracy, we focus on protecting software that runs on devices outside the cloud–like desktops, phones, and IoT devices. We recently launched Fusion AI to protect Embedded AI running on customer premises, within desktop applications, and at the edge.
This article explains why Embedded AI is growing in importance, the risks of model theft, and how to keep your models safe.
Most people think of AI as something that runs in the cloud. You type in a prompt, send it to a server, and get an answer back.
However, there are many use cases where it makes more sense to run at the edge with the model embedded into software running locally to the user or the data. This is called Embedded AI.
There are a few reasons for running AI at the edge:
AI models take a different form from traditional algorithms.
Traditional algorithms are coded (e.g., in C++) as logical sequences and compiled into machine code that executes on the edge device.
AI takes many forms. The development methodology will depend on the form of AI being implemented. Something like a rule engine or knowledge graph will be coded like a traditional program, whereas statistical approaches, like Machine Learning (ML) and Large Language Models (LLMs), require more complex implementations.
The complexity of statistical models means they are generally developed in a framework (e.g., PyTorch), much like game developers build on top of Unreal Engine and Unity to avoid having to reinvent the complex building blocks.
The framework is generic code, with the valuable IP contained in the model that runs on the framework. Models are typically a mix of data and interpreted code (e.g., Python that is deployed as source code). This makes them extremely easy to lift, analyze, and steal.
The interpreted code defines the structure or architecture of the model. Basically, how the different algorithms that make up the model are connected together.
The data defines the statistical “weights” that are calculated by training the model and applied throughout its execution as it processes the input data to reach a conclusion.
For more performant models and on resource-constrained devices, compiled code may be used in development to increase performance. This makes development much harder, and out of the comfort zone of data scientists, so it’s rare.
While there are many threats to AI at the edge, the risk of IP being stolen is the one that holds back many companies. They don’t want their hard work falling into the hands of researchers, competitors, or criminals.
For teams building embedded AI products:


Stopping the AI models from being stolen is a code-protection challenge. You need to stop reverse engineering and lifting of the model. It should not be possible to:
The model should be encrypted at rest. But real protection means using white-box cryptography at runtime to perform the decryption. A white-box is needed to protect decryption keys. Also, it will need to be securely anchored into the rest of the software so it all stays coupled to the developer’s use case.
White-boxes that are provided as developer toolkits, like PACE’s White-Box Works, allow solutions to be architected that tightly tie in with AI runtime. This minimizes any gaps where the model is in the clear between decryption and model initialization.
Strong runtime protection products, such as PACE’s Fusion, should be used to securely tie all the different components together – ensuring that the AI stays tied to the wider application’s use case. Runtime protection also stops a threat actor from attaching debuggers and other analysis tools to observe or manipulate the model at runtime.
AI models are valuable intellectual property, but when embedded into software applications, they face serious risks of theft and tampering. Running AI at the edge offers benefits like lower costs, faster response times, and stronger privacy, but it also makes models easier to copy or reverse engineer.
To protect both the technical work of developers and the business value that product managers depend on, companies must secure models at rest, during runtime, and in use. With tools like Fusion AI, organizations can encrypt models, block attacks, and tightly connect protections to their applications–ensuring AI remains both safe and commercially viable.




Download the Fusion AI product brochure to learn more about how PACE protects your AI models and allows you to maximize their value.
Want to learn more about protecting your Embedded AI? These articles are a good place to start:
Or reach out to PACE to discuss how we can secure your AI models when they are embedded into software applications.
Like most technology companies, PACE has been experimenting with AI tooling to help with software development. A lot of the coding we do is deep, low-level stuff–often close the machine. This definitely tests the AI and it’s fair to say it will be a long time before AI starts to replace our engineers. That doesn’t mean we don’t find it useful. For us, the AI tooling is at its most useful when used somewhere between advanced autocomplete and a peer programmer. Definitely a useful copilot but it’s not going to be flying the plane anytime soon.
In development environments like PACE’s, “vibe coding” isn’t about replacing skilled software engineering teams. Assisting and allowing developers to move faster, yes; full-on replacing full teams, I don’t see it.
So am I going against the tide and predicting that vibe coding will be a fad that will quickly die out when faced with real world challenges? Well, not quite. I actually see “vibe” coding taking a different direction. One where it is seen less as “coding” and more as “authoring.”
I’m not actually proposing anything new here. Sci-fi authors have been showing us this future for decades.
Take, for example, when a Star Trek character walks onto the holodeck and starts building a virtual world or simulation, they don’t open their favorite text editor and start typing out Rust code. Instead, they simply describe in plain language what they want.
"Computer, show me a beach at sunset with a gentle breeze."


The computer interprets those requirements and boom, you are on that beach.
That’s vibe coding. But Star Trek doesn’t talk about “holonovel coders,” it talks about “authors”. This is the right view point: vibing is a lot more like authorship than technical coding.
This is where vibing becomes a powerful and useful tool: when we want to create engaging, realistic, and potentially complex content. And that content can take many forms: pictures, videos, and audio but also web sites and apps.
The Star Trek example (non-trekkies please bear with me) also makes another prediction that I believe is on the cusp of becoming true. Movies and television content will start to merge with gaming. Increasingly, we won’t sit watching a predetermined sequence of frames. All content will become personalised; reacting to us.


If this prediction is true, then content distribution approaches will have to change. Our playback devices (whether screens, VR headsets, or holodecks) can not continue to be dumb clients. The overhead and latency of doing all the processing in the cloud and just streaming the result is not viable for personalized content. Just like with games today, the runtime engines, building blocks (characters, scenery, physics models, etc) and the story will be downloaded to our local devices. Our local devices will then do the work of generating each scene and playing the story to us. Especially as we “vibe author” the story we want to play.
This is going to rely heavily on client software (applications) executing a network of interconnected AI models. AI running inside applications is called Embedded AI.
Where there’s content, there are invariably pirates wanting to monetize other people’s hard work. PACE has spent 40 years defending our customer’s valuable intellectual property.
For our vibe-coded virtual worlds, pirates will have to come up with new attack vectors. CDN leeching and torrent downloads don’t make sense when the content is personalized. These attacks rely on each consumer watching the same content.
History shows that piracy that provides an identical experience to the legal version will always be much more successful than one that offers poor-quality play-back. For our vibe-authored worlds, removing the personalization is the equivalent of the dodgy, handheld camcorder-captured VHS of a movie. Who wants to watch that when the 4K stream is available?
That means piracy in the future will shift from stealing and distributing streams to stealing and distributing the assets that make up the content: the AI models and associated data.
If our prediction is correct, and vibe-authored content becomes the norm, then the good news is that we are already one step ahead of the pirates. Under the hood, “video” content starts to become much more like software–and we know how to protect that.
As the pirates adapt to new forms of content, we can leverage proven software and data protection techniques to defend against them. This includes PACE’s code protection security suite, called Fusion, and white-box cryptography products like PACE’s White-Box Works.
If you are developing AI models or assets that will be used in software applications, please reach out to discuss how PACE can protect them, keeping you one step ahead of the pirate.
All images in this article were vibe-authored.
Most software developers have heard of code obfuscation. It’s a technique that takes well constructed, easy to follow code and turns it into something that is difficult to understand. The aim being to stop a reverse engineer (a hacker) from reading the compiled code (static analysis) and discovering how it works.
This article introduces a method for software developers to go beyond obfuscation to protect critical algorithms in code.
Obfuscators are provided as developer tools. Typically they either apply obfuscation as part of the software build pipeline or it is applied to the software binary after it is built.


More basic forms of obfuscation strip out human readable text that is left in the software after it is compiled. While more sophisticated tools will alter the software’s instruction sequences to make them harder to follow–trying not only to confuse the hacker but also the powerful reverse engineering tools at their disposal.
PACE Anti-Piracy, an expert in software security, would never advocate obfuscation on its own as a strong security measure. Working with internal and external “red hat” teams we know that obfuscation only keeps the hacker at bay for so long. But we also know that when sophisticated obfuscation is coupled with other security measures, such as protecting binary integrity with anti-tamper and anti-instrumentation techniques, there is a multiplier effect and all the techniques work together to create something much stronger than the sum of their parts.
PACE specializes in providing technology solutions to protect our customer’s software IP. We stop software applications from being pirated and we stop value algorithms from being reverse engineered.
One of the tools in PACE’s arsenal is a white-box cryptography product called White-Box Works.
White-box cryptography has historically been used to protect cryptographic keys in software. If a hacker can analyse a software application, then they can see any cryptographic keys that are embedded in that software. While it is recognized as best practice not to hardcode cryptographic keys into software, sometimes it is unavoidable. White-box cryptography was developed to solve this problem and has been proven in markets such as video DRM and mobile payments.
White-box cryptography is successful because it stops hackers from understanding software algorithms and the data on which they operate within a white-box environment. A white-box environment is one in which a hacker can see every instruction execute, and every memory read and write. Nearly all software that is deployed off-premises should be considered vulnerable to attack under white-box conditions.
To achieve secure execution where secrets can stay safe for a long time under white-box conditions means going far beyond typically obfuscation techniques. Commercial white-boxes use approaches like mathematical masking so data is near exposed in the clear, and multi-dimensional misalignment to defend against side channel attacks.
PACE has built upon these techniques to move white-box cryptography beyond cryptographic key protection and to use it to protect critical software algorithms and the data on which they operate from reverse engineering.
This is useful to any business that is developing and then licensing software algorithms. Common examples that PACE encounters include digital twins, audio processing, object detection in images and videos, industry control, and medical devices.
The process is straight forward for a developer:


The output of the tool is functionally the same as the algorithm defined by the developer but the operations of the algorithm have been transformed into code that will confuse even the best hackers.
This allows business critical algorithms to be used in software that is deployed into the wild without them being reverse engineered by competitors, criminals, or curious academics.
Protecting your critical software algorithms is no longer just about obfuscation. By leveraging advanced white-box cryptographic techniques, developers can go beyond obfuscation to secure their most valuable intellectual property against even the most determined attackers.
To learn more about using White-Box Works to protect your algorithms from reverse engineering, contact us.
Not all software has the luxury of running as a service. In many cases software has to run at the edge. This is particular true in media & entertainment. For the purposes of this article, the “edge” is stretched to its widest possible sense to include on-premises servers, desktop PCs, mobile apps, and embedded systems. At PACE, we call this “the wild,” as the environment is no longer under the control of the software developer.
Reasons for running at the edge include:
Software security exists to protect software in the wild. It enables software to protect itself—stopping piracy, thwarting reverse engineering to extract intellectual property (IP) and software secrets, and attesting that the runtime environment is as safe as possible.
Software security is essential to protecting the media and entertainment industry and the highly valuable content it creates.
Securely delivering video and audio content to consumer devices means encrypting the content from Content Delivery Network (CDN) to screen. Any encryption is only as good as its key management. With content distribution, the decryption has to happen on the consumer’s device—as close to the screen as possible. That poses a key management challenge: how do you keep the key safe on an insecure device? Often a secure hardware chip (e.g. a secure element) is used for this, but many delivery platforms won’t have access to secure hardware. That means using software security solutions like white-box cryptography.
PACE has been working with DRM vendors to upgrade the security of their DRM implementations.
In many cases, the tools used to create and manage content are as valuable to their developers as the content they are used to create. If the revenue from the tools is compromised through piracy or unlicensed usage, then the developers do not have the funds to continue to invest in the tools. Protecting this revenue is the job of software licensing. Licensing allows the software IP owner (often the “publisher”) to control access to their software, only allowing licensed users to use it. The best licensing platforms also secure the software IP from reverse engineering and firmly anchor the licensing to the software package. This stops “cracks” from appearing.
PACE has been working in media and entertainment for decades to provide secure and trusted software licensing to some of the biggest players in the space.
If you want to make a CISO (Chief Information Security Officer) twitch, mention “API abuse” to them. They understand the damage—in terms of money, disruption and brand—that can be caused by a cyberattack that exploits exposed APIs. The traditional approach is to build defenses behind the API. The cybersecurity equivalent of having a security guard behind your front door.
At PACE, we believe it is also important to get in front of API Security. Our security tools allow for the secure authentication of software running out in the wild, like video players on consumer devices. This means only software you can verifiably trust has the key to unlock your front door.
Not all AI models run behind data center firewalls. As was recognized at this year’s Mobile World Congress (MWC), Edge AI is one of the most exciting areas of technology development. Running AI at the Edge brings new security challenges. How do you stop someone from accessing your model? Access means they can:
PACE has been working with customers in media and entertainment, and beyond, to protect their AI models deployed at the edge. We help them to securely encrypt the model, and to firmly anchor the model to the rest of their software package. This keeps the contents of the model secret and means it can only be used for its intended use case.
Software running at the edge often contains interesting and business-valuable algorithms. After all, one of the reasons for edge computing is to run processing as close to the action as possible. Like AI models, running algorithms at the edge exposes them to reverse engineering and manipulation risks, as well as lifting attacks. For many companies, the algorithms they develop are the technological moat that keeps them one step ahead of the competition. The longer an algorithm remains a trade secret, the more value the company builds and the more time they have to invest in taking the next step.
PACE provides our customers with tools to protect the value of their algorithms.
At PACE Anti-Piracy, we specialize in software security—helping companies protect their intellectual property, secure their software in the wild, and prevent secrets from being extracted.
Whether it’s safeguarding DRM content, securing AI models, or locking down critical algorithms, our solutions are built to defend against piracy, reverse engineering, and cyber threats.
If you’d like to learn more, reach out to us or schedule a meeting at the upcoming NAB Show 2025. Let’s talk about keeping your software secure.
PACE spoke about code signing at the 2024 droidcon London conference. While the talk focused on the Android platform, the key takeaways were applicable to software developers targeting any modern operating system.
All Android apps must be code signed to run on a device. This is performed either directly by the developer or through Play app signing. Despite every app needing to be code signed, the processes around it are increasingly abstracted away from the developer. This has resulted in code signing becoming shrouded in mystery.
Most modern operating systems use code signatures. These are a cryptographic hash of the software binary and other assets that make up the application. The signature is embedded in the application and is verified by the operating system during installation or launch.
Verification checks whether the binary or the assets have been modified since the app was signed. Only if they have not been modified is the signature valid.
Android won’t install an app without a valid signature.
Signing identifies the last person to modify the app. Usually, that’s the developer. However, it could also be a separate release team or someone trying to hack the app.
Android doesn’t act as a certificate authority or keep a list of valid certificates. It is perfectly valid to use a self-signed certificate.
The Android operating system uses the signature to imply ownership of the app once it’s installed. Responsibility falls on the last person who touched it.
Firstly, you can’t upgrade an app if the certificate changes. So this gives the user some confidence that version 2 has come from the same developer as version 1. This gives some defense against phishing attacks that tempt users to install a “special” version of an app. Often these special versions are trojans for delivering malware.
Secondly, the signing certificate is used when defining the sandboxing for each app installed on a phone. In practice, that means it is easier to have two apps talk to each other if they were signed with the same certificate. That allows the developer to make choices about how their apps interact, but another developer can’t easily break down the sandboxes without resorting to hacking techniques.
Historically, the process of signing an Android app (the APK) for publication was fairly straightforward.
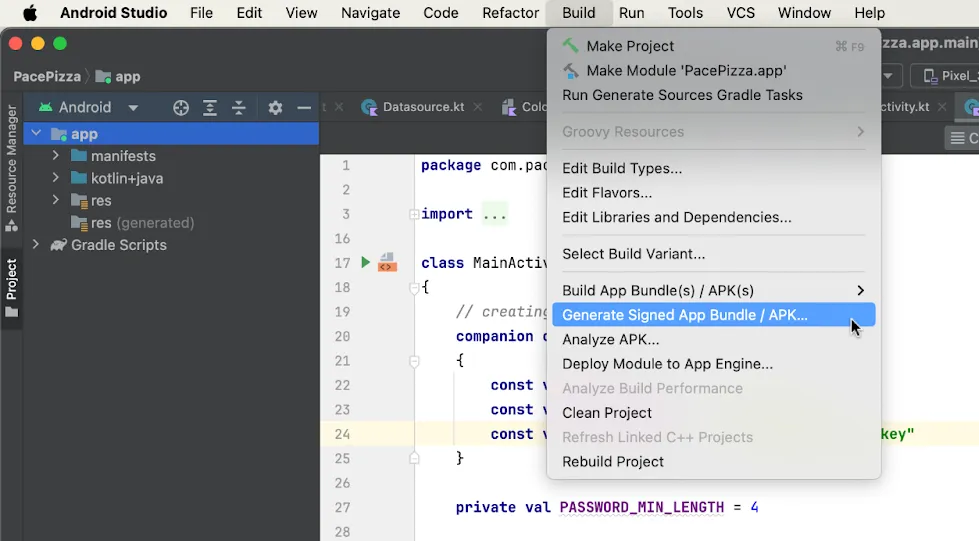
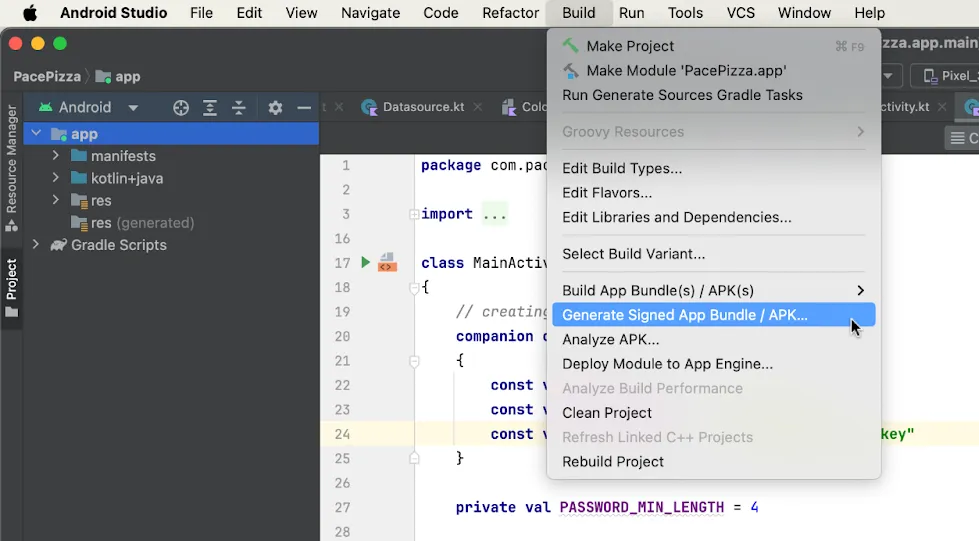
Android Studio even simplifies the process and signs the APKs for the developer; either quietly when pushing builds to phones for testing during development, or when explicitly asked to create a signed APK.
Since that process was developed, the Android developer ecosystem has evolved. Firstly, developers don’t upload APKs to Google anymore. App Bundles (AABs) are uploaded instead. Secondly, Play app signing (“Play signing” for short) was rolled out.
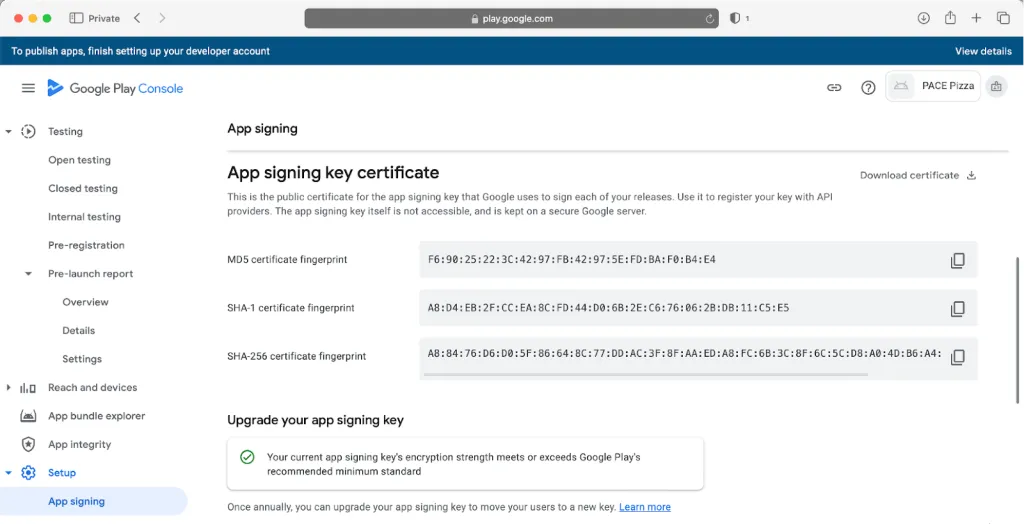
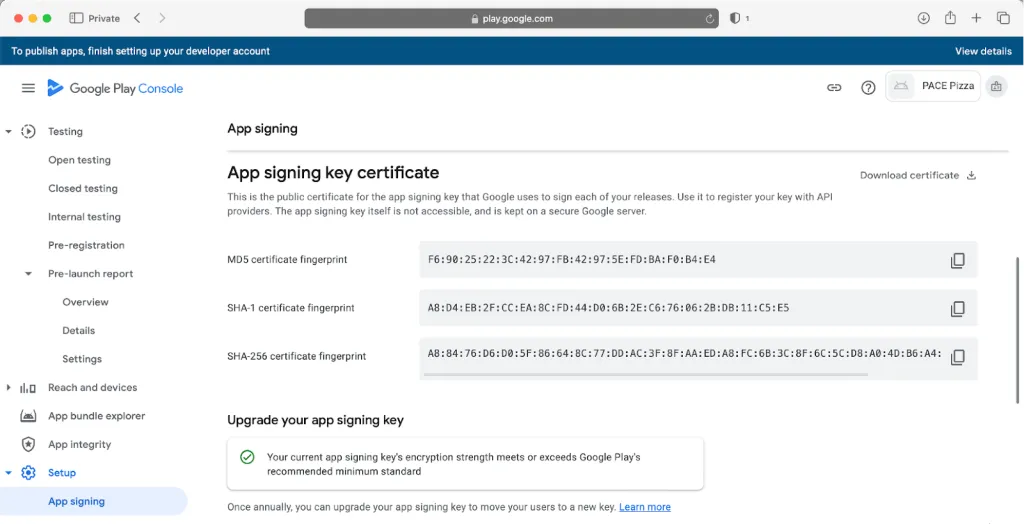
With Play signing, Google re-signs the app before delivering it to users. So the APK the user receives isn’t signed by the developer’s key, but by a key that Google manages on the developer’s behalf. In 90% of cases, this key was even created by Google.
The key the developer originally signed with is now called the “upload” key. The APK signed with this key is still valid for local testing.


A lot of developers don’t realise that re-signing is happening in the background. But if Play signing is enabled, then Google is re-signing the app.
In fairness, the developer console has improved at explaining the developer’s choices. There was a period when Play signing was forced on for all new apps.


Having Google manage the keys is usually beneficial; and having the app re-signed doesn’t typically cause any problems. However, if the developer is relying on the signing certificate for anything, then they need to accommodate this re-signing. Common dependencies on the signing certificate are for security reasons, e.g., to make sure the app isn’t being re-signed by a hacker.
If the developer needs details of the signing certificate Google is using, they can find it in their Play account.
What about AABs? An AAB is a bundle of assets that Google uses to create tailored APKs for different devices. If Google is creating the APKs, then Play signing means that Google has the ability to sign them too.
There’s a common misconception that just because code is signed, it is secure. That is not the case.
Firstly, anyone with access to the freely downloadable developer tools can re-sign your code, using the same process as the original developer and overwriting the original signature.
Secondly, code signing does not protect your code from modification or reverse engineering. Signed or not, a hacker can open the app in static analysis tools. Because the app can be re-signed, it is easy for a hacker to take control to make modifications or dynamically analyse the code.


Platforms (like Android) implement code signing to protect the broader ecosystem, not the individual apps within the ecosystem. Android uses code signing to define the boundaries of the sandboxes—limiting the reach of bad actors.
Some platforms go further, using code signing to allow only trusted developers to deploy apps or modules in the first place. This is a use case supported by PACE’s code signing platform, which is a PKI-based solution for code signing and validation.
Code signing does not stop someone from reverse engineering your code or finding secrets within it. Developers must take responsibility for code protection:
Every app in the Android ecosystem must be signed to be installed on a phone, although this process is often abstracted away from the developer. Code signing protects the Android ecosystem—not the individual app developer.
Developers who store sensitive data or algorithms in their apps need additional measures, such as PACE’s White-box Works tool, which provides strong protection to stop software algorithms from being reverse engineered and cryptographic secrets from being exposed.
To learn more about using white-box cryptography in your software, contact PACE to talk with our experts.
Software publishers and creative users alike recognise risks to their Intellectual Property (IP). While software publishers can use secure licensing solutions like iLok Licensing, for many of these creative users, any leak of their content will significantly impact their business’s viability.
A common solution to protect content is to adopt an “air-gapped” architecture, where a machine, internal network, or even an entire building is completely disconnected from any internet connection. This architecture by its very nature prohibits cloud-based Software as a Service (SaaS) solutions, presenting a challenge for Software Publishers who rely on cloud-connected licensing to manage their IP.
When deploying software into air-gapped environments, there are two categories of users to consider:
A good licensing solution allows end users to access their software without compromising the IP security expected by the software publisher.
The vast majority of today’s Software Entitlement Management and Cloud Licensing solutions are ill-suited to IP-conscious end users. These tools can and do allow large corporations to have their license entitlement kept within the guidelines of the respective licenses, but their need for a constant (or even periodic) internet connection is fundamentally incompatible with air-gapped environments. Software publishers need to consider whether this limits their addressable market.
Application software is often used in an air-gapped environment, connected to nothing but a secure internal network, on which a team’s work can be shared and archived prior to breaking cover, perhaps as 3D Printed components or a new Streaming TV series. In this scenario, how does the application software’s publisher ensure it is used according to license agreements?
One option is using a Cloud License (SaaS) service provider’s on-premise license server inside the air-gapped network, but this often entails significant IT integration challenges, making it suitable only for large corporations. And who wants to set up a new server just so their team can use a new software package?
The licensor then typically sets a limit (e.g. 50) on the number of licenses the server can allow, usually using a “license file”. In case that server goes down, they will traditionally provide a second “backup” server, making everyone happy—especially the Corporate User, who now has access to 100 legitimate licenses for the price of 50…
Alternatively, a licensing solution with a hardware authentication component, which doesn’t rely on an always-on internet connection and cloud authentication, is a solution a number of our security-conscious users are happy to adopt.




Download the iLok Licensing product brochure to learn more about how PACE's software licensing platform protects your IP and allows you to maximize your value.
Let's explore PACE’s alternative to bending a cloud SaaS product into an on-prem solution.
PACE Anti-Piracy offers the iLok USB as an industry-proven solution for air-gapped environments. This tool provides software publishers with reassurance that end users can only run their software in the presence of a trusted iLok containing their software license.
Every iLok USB can store many licenses. The software publisher’s usage rules are securely held on the iLok and cannot be circumvented or overused, but authorized users can make use of the licenses as required upon request from their administrator.
Once a license has been deposited onto an iLok USB, there is no need for an external internet connection. The protected software application or plugin communicates with the iLok USB and is authorized to run. As the iLok USB is an active security device, this is a highly secure operation.
Sharable licenses (often called multi-seat or network licenses) provide flexibility in licensing and simplify license management, especially for users with large numbers of licenses for the same product in institutional settings. Inventory control and ease of deployment across large networked facilities are key features requested by the administrators of large numbers of iLok accounts.
For teams that prefer not to have USB keys for each user, PACE offers network options via iLok Server.


iLok License Server (ILS) permits an administrator to set up their own shareable license server in the air-gapped network and allow multiple client computers to use licenses that the administrator is sharing. An iLok USB is plugged into this server. The licenses are not held on the server itself, but on the iLok USB—the server merely allows licenses to be shared with the correct users.
The server is as simple to set up as a desktop application and access is over the regular network, simplifying the process and avoiding the need for additional costly servers. An authorized individual can then manage the licenses and users' access to them, allowing multiple client computers to use licenses held on a single iLok USB. This model is so much easier than integrating a pre-configured server from a vendor into your network, that we have many hundreds of instances running in educational environments, set up by teachers themselves.
PACE also supports multi-seat sharable licenses to help users easily manage licenses for multiple copies of the application software across their air-gapped network. Setting up the server and the connection from client computers to the server is simple, with no additional network configuration required. Passwords can optionally be set to limit who can use the sharable licenses. From large facilities with hundreds of licenses and seats, to smaller facilities using just a few individual licenses, sharing licenses over a network is simplified and remains secure. Real-time statistics on license usage are provided, and the statistical data, protected by a password, can be accessed remotely.
To use iLok License Server, a user can contact the publisher offering the shareable license in order to obtain the necessary ILS license.
PACE’s unique Zero-Downtime (ZDT) technology, available as an optional purchase for the iLok USB, can be used to guarantee continuous access to licenses. This combination ensures that the end user’s team can continue to create without interruption, while reassuring the software publisher that their IP is protected.
PACE Anti-Piracy through decades of experience understands the critical importance of protecting IP in a rapidly evolving landscape, while ensuring innovative licensing solutions deliver for the end user and publisher alike. iLok USB and iLok Server are proven, practical, secure solutions to the IP protection conundrum of air-gapped environments, protecting both publishers and users creativity.To find out more about PACE’s solutions, reach out to our team.
On the 14th of August, Apple announced that it was opening up Near Field Communications (NFC) and the Secure Element (SE) on iPhones to third parties. This was the news that the payments industry and many others had been waiting for. But is this as revolutionary as it initially seems?
I’ve been involved in mobile payments since 2010. Even in those early days of technology demonstrators and pilots, the big question was iOS. Many banks I spoke to were interested in developing their own wallet, but only “once iPhone is possible.”
It wasn’t just payments. I was lucky enough to be part of one of the first hotel mobile room key pilots. As the NFC antenna on iPhones was reserved for Apple Pay, the whole project moved to using Bluetooth for phone to door lock communication. It’s now the standard in hotels, but back then the room locks were NFC-only resulting in a massive infrastructure upgrade.
So, on the face of it, Apple opening the NFC and SE is an exciting development.
Beyond the initial announcements, details from Apple are limited. A lot of the coverage to date has assumed that the openness Apple will provide will be similar to how Google opened the NFC on Android in 2013. I don’t read the announcements that way. From what we know, I think Apple has a different approach in mind.
What’s the Android model? Google provides Android apps access to a device’s NFC antenna through an interface called Host Card Emulation (HCE). This allows the rich OS application (a standard Android app) to send and receive commands over the NFC antenna in the format a payment terminal will understand (a protocol called ISO7816-4).
This is a very flexible model that makes it easy to scale wallet applications in the market. All the end user has to do is install an app from the app store.
There is no security built into this deployment model. The app is just an Android app. That means the software developer needs to use technologies like strong code protection and white-box cryptography to meet the payment industry’s security requirements.


In July, when Apple reached an agreement with the European Union, the approach they agreed on mirrored Android’s HCE model. This is only available within the European Economic Area (EEA). The approach Apple is proposing for other geographies is different.
From what I can tell from Apple’s press release and public developer information, Apple is not planning on giving rich OS apps (i.e. normal iOS applications) additional access to the NFC antenna. Apple’s proposal is to allow third parties to develop applets which Apple will install and provision to the iPhone’s SE on-behalf of the third parties.
Applet’s are small computer programs designed to run within the Javacard environment of a SE. The SE is very similar to the chip in your credit cards, and keeps the program and its data safe from prying eyes.
The installation and provisioning of the applets will be performed by Apple’s Trusted Services Manager (TSM). In this way, Apple maintains the security of SE as Apple keeps full control over it and the software it’s running.
This means any third parties wishing to use the iPhone’s NFC interface for contactless transactions will need to develop an applet, give the applet to Apple, and then develop a companion iOS app that communicates with their applet. Apple will install and provision the applet to a user’s phone when the companion app requests it.
And that’s just the technology stack. There’s also geographic restrictions, security lab audit requirements and Apple’s fees for accessing the SE. Nevermind that third parties will need to convince users to move away from the excellent user experience that Apple Wallet offers.
So why would a third party consider developing a solution? Firstly, Apple has now provided a way to implement new use cases, ones that aren’t supported through Apple Wallet, so for some third parties, this may be the only way to provide their services on iPhone. Secondly, by building their own solution, third parties have a product that they control and can manage the user interaction. That means the customer engagement is wholly within their interfaces and they can build differentiation and innovation into their product to separate themselves from competitors.
Information is limited at the moment, but Apple’s plan sounds similar to the embedded SE announcements from phone manufacturers in the early 2010s. These were quickly forgotten in the excitement of HCE.
Outside the EEA, this is a more complex ecosystem for third party developers than is available on Android. Interestly, inside the EEA due to regulatory pressure, developers will be able to choose between the two models.
No-one knows what the future holds, but one thing is certain: PACE has customers and partners who are excited about the opportunity more open access to the iPhone’s NFC brings. Let’s hope it truly does turn out to be revolutionary.


Taneli Malinen sees things differently. Literally. As a production and simulation expert, he’s been building software and advising companies to see their processes in the VR space for years. He helped found Jetecon, a 3D simulation technology company that allows companies to be more productive through the use of VR and simulation.
Jetecon was founded in 2007. We started consulting and doing simulation models of different types of value chains and logistical systems. So for example, a warehouse manufacturing plant assembly process. We would create a detailed model of this which would allow the company to then run a digital twin.
From there in a computer environment you could check things like how fast a batch would go through a factory and how well that factory performed.
We were basically just two people for a couple of years. But we noticed right away that this was very difficult to scale. It's a very niche business. So we thought about making something more scalable, i.e. software. So in 2018 we came up with the idea that with software you could create your own VR environment to explain a predefined process. Something that felt “game-like” but was based on learning. For example if you would like to teach somebody how to change a car tire, you could then do it in our software where you have that tire, and the bolts and the tools and then create the process. You learn the steps via the software in the correct environment.


This works well for certain companies that teach people to use their products. They can use our VR environment and create, for example, problem situations and then within the environment, teach people how to solve the problem.
This is not a new idea in VR environments, it’s been around a long time. The difference is that with our software you are able to do more complicated tasks that require a bit more learning in a more efficient manner that solidifies the process.


Yes. For now we are working with manufacturing assembly factories. But it can apply to any industry. If you have an automated system there are a million things that can go wrong. So you're going to use our software to create all these different scenarios of what could go wrong and then learn how to solve them. What’s great is that it scales. When people change in the factory you still have this VR environment where you can easily train new employees. The biggest market at the moment would be in the services business. For example, American companies that have products in Finland but don't really have factories or engineers. They have very small support teams locally. For example, with Caterpillar you have these very big trucks. And when there's a problem you have to get somebody from somewhere in the States to come to a location or at least do some videos and send them to the customer. It’s very slow. With our software they could learn to solve the problem in VR and get the truck up and running much faster.
Yes after troubleshooting what the actual problem is. Let's use an endoscopy or a colonoscopy, for example. No doctor goes in and says “I see a polyp” and fixes it right away without training. And that training can happen in VR before they train on patients. Our software is definitely a B2B solution for many industries.
Yes. Absolutely.


Everything is built on Unity. And if I give you the software, it's basically a Unity application. It's very simple. Basically in our software, the main idea is to select what you want to move and then you define where to move it or how to move it. So let’s take the example of repairing the truck. The main idea is to have parts that are 3D in a VR world. You can add or you can remove various parts and steps. I always say it's a movie. So you create your own movie of what to do and what to do it with - then you can animate it. For these types of three dimensional workflows we use Unity.
We use PACE to wrap it and to protect it. From there we can distribute so we use PACE to license everything via iLok. So when we distribute our software we are thoroughly protected.
We could have done this ourselves but it would have cost much more and PACE has a lot to offer us in the long term. It’s a very good environment. It’s a turnkey solution to protect our software and enable our distribution in the most flexible way.
We looked at many other solutions, but PACE had a much more flexible system of handling and distributing and doing different types of packages of the product. The pricing wasn't the cheapest. But I think it's the most competitive and they understood that we were a start-up and priced accordingly. PACE was the best choice.
We have felt like there was someone with us every step of the way. From the sales contact to the technical support, we’ve had a very good experience. They really listened to our needs and cost concerns. We’ve also been working with them to help test products and that has also been a good experience.
The first time I used it I spent maybe 15 to 20 minutes checking some documentation from the internet portal, and I was able to use it. It's pretty simple. I think compared to other solutions that deal with complexity and need flexibility, the quality of PACE works best. It’s pretty user intuitive and everything so far has gone smoothly.
We could do a basic level of protection but in the long term, I don't see how we could ever get there. We should focus on our product. As things scale, PACE already has all the tools that we need. We couldn’t scale without PACE. It secures our future.
Jetecon OY is a company specializing in developing production processes and the logistics in the value chain
Our experts have a solid knowledge of the field and years of extensive experience in simulation technologies and their successful utilization in various industrial sectors. Our operations are based on the described approaches and the comprehensive use of modern technology.